The HackRF One is an awesome entry platform into the wonderful world of SDR. I do, however, want to point out one thing to be careful about: operating at too low a sample rate.
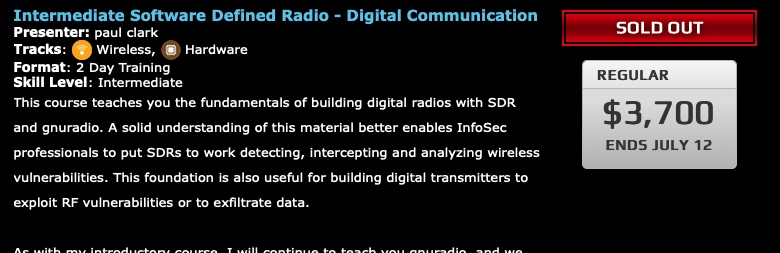
In a recent class I was teaching, I introduced a new project: one in which students transmitted a simple triangle wave at a specified frequency. As good RF citizens, we of course transmitted these signals at very low power, and for short duration in an appropriate band.
I had tested this exercise several times prior to adding it to the class syllabus, but during the class itself, something went wrong. About half of the students were able to generate a transmission that could be received, demodulated and identified as a clear triangle wave… and about half couldn’t. Since each student had their own HackRF One, we swapped hardware and tried executing the flowgraphs again. Sure enough, all of the flowgraphs worked with some of the HackRF devices, and all of the flowgraphs failed with the other HackRFs. Since we were nearing the end of the class I didn’t have time to do much live debug, but it sure seemed like some of the HackRF boards were behaving differently than others.
After I got back to my lab, I did some research as well as contacting Nooelec – where I had bought the boards. A very quick response from the Nooelec folks (thanks!) led me to assume that I might have burnt out the RF amplifier chip by exposing the HackRF to excessive RF energy. Nooelec has seen this a number of times and recommends putting a 10 dB attenuator in series with your antenna. It’s easy to miss this note, but documentation does state this:
https://github.com/mossmann/hackrf/wiki/HackRF-One#receive-power
I then prepared for PCB surface mount surgery on one of my HackRFs using the following info:
http://www.t4f.org/articles/repairing-the-hackrf/
Before I made the incision, however, I decided to check a few more things. I set up an Ettus B200 in receive mode and tried to fiddle with several HackRF boards in transmit mode. The Ettus board has better ADCs, a better RF front end… pretty much better everything than the HackRF. My hope was that I could figure out a little more about the failure mode of the HackRFs. After poking around for a bit, I came to a startling conclusion: the boards were fine, I just made a boneheaded mistake!
You see, I was a little concerned about the performance of the laptops that my students might be bringing to the class, or that they might be trying to use a VM for the class exercises. As such, I had the not-so-brilliant idea of reducing the sample rates of the class exercise to 1 Msps. The documentation recommends a minimum sample rate of 8 Msps, but I’ve always played a bit fast and loose with that figure without too much trouble. Even as low as 1 Msps, I’d often gotten usable results.
When I upped the sample rate to 8 Msps, however, it was clear that the boards I had thought broken were just fine:

Even as low as 2 Msps, the triangle wave was clearly visible. At 1 Msps, though, things started to break down for some boards:

But not others:

After all of this, I took a look back at the specs, and sure enough, I noticed the 2 Msps is the listed minimum sample rate after all.
A happy, if slightly embarrasing, ending.